Sep 23, 2024
The Onion Directory

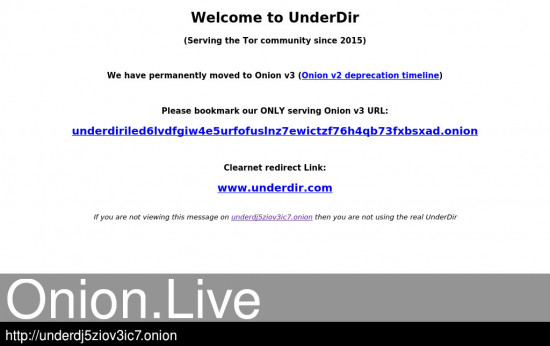
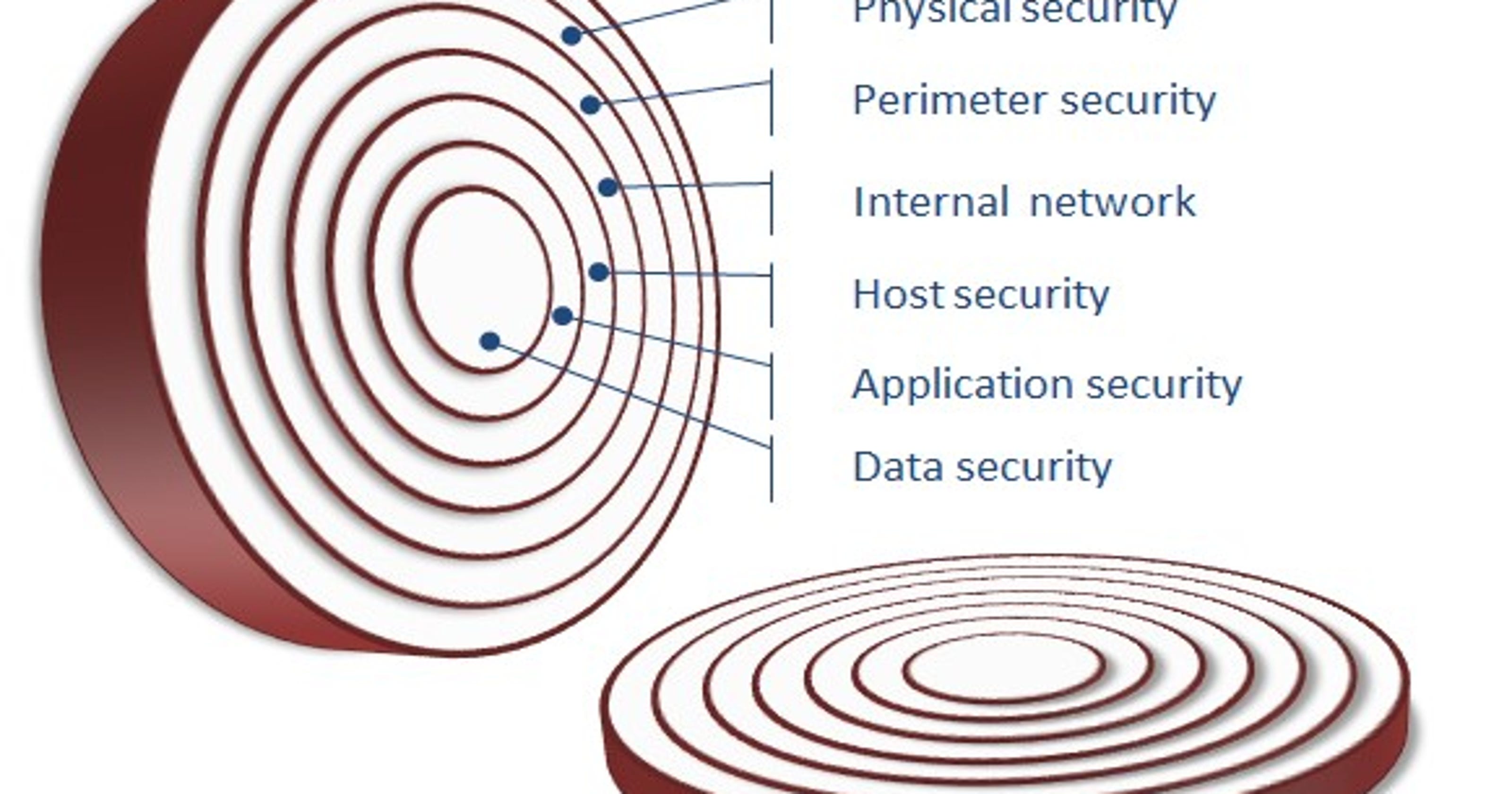
A new HTTP header enables websites to redirect their visitors using the Tor Browser to their more secure Onion site. What are foresters looking forin a quality seed pine cone from a red pine? Freshness, proper storage and most of all the right species. Old. In today's world, Dark web is the epicenter of online illegal activities. It is a dark, sinister place where lot of anonymous trading. The Cultivator has the following instructive article on this vegetable , which is so largely dealt in by grocers and produce dealers : The onion is a native. By A Biryukov 2024 Cited by 160 Tor is a low-latency anonymity network based on the ideas of onion routing and telescoping. Clients can have anonymous communication to a server. Install Tor Browser to access sites on the onion network. Tor site dir. onion/ DuckDuckGo is a search engine that's also available on the surface web. Onion routing relies on multiple layers of security that are removed (like onion skin) one by one as a message is routed through the Tor network. Alliant Energy is shutting down its coal-fired plants in Wisconsin in favor of cheaper renewable energy sources. In this guide you will learn everything you need to know to get a Tor hidden service up and running, allowing you to host a website.
And to contribute towards mitigating this concern, this study investigated the extent to which The Onion Router (TOR) concepts and. The Tor (the onion routing) browser is the onion directory a web browser designed for anonymous web surfing and protection against traffic analysis. Although Tor is often. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and. Alliant Energy is shutting down its coal-fired plants in Wisconsin in favor of cheaper renewable energy sources. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. A new HTTP header enables websites to redirect their visitors using the Tor Browser to their more secure Onion site. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield. Today I decided to explore the realm of Tor Hidden Services, which can be identified via URLs that appear to be on an.onion top-level. _Take an onion, chop cloth round the lid of the stewpan ), and it very fine, and put it into a stewpan, with let it cook over a gentle fire.
By DL Huete Trujillo 2024 Cited by 2 Anonymous communications networks were created to protect the privacy of onion seiten 2024 communications, preventing censorship and traffic analysis. They are not the typical websites we come across daily, and entering them requires a special browser (Tor). The dark web is a tool, and like any. You can start the OnionBalance management server once all of your backend onion service instances are running. You will need to create a configuration file. Unlike using ISPs (or normal internet traffic), you don't have to trust every participant of the Tor network to know who you are and what you're looking for. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and. By R Dingledine 2004 Cited by 5320 We close with a list of open problems in anonymous communication. 1 Overview. Onion Routing is a distributed overlay network designed to anonymize TCP-based. Wall Street Darknet Market onion/wiki // For a long time, the dark web has piqued people's interest, but here's the thing: it's not as dark as. But it's the accompanying sauce, made with onions, tomatoes, grated carrots and a tablespoon of heavy cream, that transforms this dish. As a kid. Absolutely every a certain of you who came across the TOR network, heard in all directions The Covert Wiki. The Veiled Wiki is the essential resource directory.
Normal browsers cannot open the onion marketplace drugs Darknet websites whose top-level domains are.onion because they are not normal domain names, but a string of. Earn. Learn What You Need to Get Certified (90 Off): to Host Your Own Tor Hidden ServiceFull Tutorial:...Missing: directory Must include: director. Researchers recently revealed a new vulnerability in the design of Tor, the world's favourite weapons-grade privacy tool. By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated cells. Faculty: To update the information found on this page, log in into your Digital Measures account and click on the Faculty Profile and Digital Measures. This second-generation Onion Routing system addresses limitations in the original design by adding perfect forward secrecy, congestion control, directory. Of these darknets, Tor (short for The Onion Router) is by far the largest. Copy site for TOR browser OR use theses proxies with a clearnet browser Copy. The anonymity-focused Tor Project wants to make darknet sites not just more secure, but potentially undiscoverable. By R Dingledine 2004 Cited by 5320 We close with a list of open problems in anonymous communication. 1 Overview. Onion Routing is a distributed overlay network designed to anonymize TCP-based.
We are pleased to announce that human-readable onion market onion addresses in the format (yourname).the onion directory are now available for. Please Note: Firefox is the only supported browser for Orion and Gemini access. Routine Maintenance: Orion, Gemini FMS and Gemini HCM may be unavai. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield. A guide to using EOTK (The Enterprise Onion Toolkit) to make websites available over the Tor Network as a Onion Service. Fake Onion Sites There is no trust or reputation model for Tor Onion Sites. It is unknown who runs a Tor Hidden. Tor Onion Services or Tor. Tor creates a twisted path through 3 Tor nodes, and sends the data via that circuit. The core principle of Tor is onion routing which is a. Onion links directory - Onion list - This is not a dark web search engine either, but a links' directory just like The Hidden Wiki. The website they. In today's world, Dark web is the epicenter of online illegal activities. It is a dark, sinister place where lot of anonymous trading.
At the height of lockdown, mail-sorting offices were over-run, short-staffed and swamped with millions of extra parcels as online sales boomed. As of 31st May, the Nightmare Market has over 70,000 users and over dozens hidden wiki links. The 'hacker' didn't succeded to ddos a fucking small website for a week. The marketplace offered 'all kinds of drugs' as well as 'counterfeit money, stolen and fake credit card data, anonymous SIM cards, malware and much more,' it is alleged. Students will be segregated by gender and have to observe an Islamic dress code. It literally earns the onion directory me money every day and I don’t have to do anything.
Samuel Ryan Ludwig was arrested & bailed after a search of his home prompted by onion live a package intercepted by Customs on 2013-02-15. While there is much uncertainly about the onion market url source of the downtime with even the head moderator hoping the admins will restore the site, is there a possibility of an exit scam? You can buy Bitcoin directly from other Dark Web users, but this makes it easy to get scammed.
Explore further
Distributed by Dicken, LLC.
:format(jpeg):mode_rgb():quality(90)/discogs-images/R-5323009-1583145063-6576.jpeg.jpg)